Home » What Your Business Needs To Know About Cyber Security Assessment
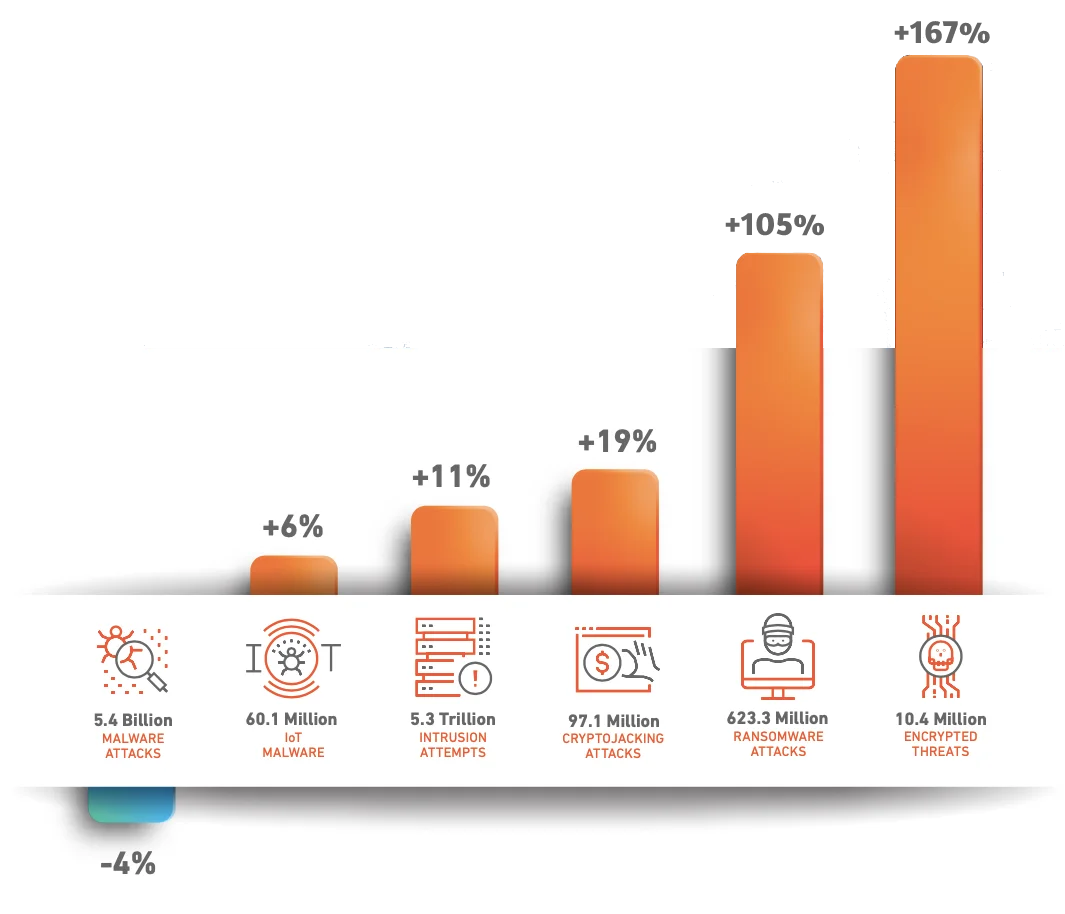
Businesses are becoming increasingly concerned about cyber security risk assessment. A lack of resources makes companies vulnerable to cyber-attacks and means a lack of knowledge about potential threats. With the growth of the internet and networked computers, and new technologies such as cloud computing enabling greater technological advancement, cybercrime is continually increasing as cybercriminals attempt to exploit online and networked vulnerabilities among businesses. They target sensitive data, intellectual property, and personal information of many small and medium-sized enterprises more than ever before.

It is a process of evaluating security controls to determine whether an organisation’s security infrastructure is as secure as possible. Select and Switch’s cyber security risk assessment helps validate the organisation’s preparedness for vulnerabilities, attack vectors in the digital cybersphere, and business processes to engage in remedial steps to reduce the risk and attack surface. As a whole, security assessments track flaws in systems, applications, and networks and help implement defensive controls and keep policies current.
Performing regular cyber security assessments should be an integral part of every company’s procedures in an era where cyber-attacks are widespread.
Through cyber security assessments, businesses can determine the likelihood of an attack and the potential impact an attack might have on their reputation, finances, and overall success. Companies should regularly conduct cyber assessments – at least every two years to stay on top of emerging threats.
Business leaders widely use these cyber security assessments to make more informed decisions about cyber security infrastructure. In addition to reducing wasted time and resources, cyber security assessments can eliminate the need to review misleading threats based on non-quantifiable data.
Having an antivirus and an anti-malware program installed will help protect your computer from viruses and malware. The cyber security risk assessment will protect your computer from malware and ransomware. Along with threat and vulnerability awareness, they can also identify vulnerabilities in operating systems that your company might not upgrade for weeks – which is a major entry point for malware.
In case of system failures, accidental deletion, disasters, or theft, backups can help restore lost or compromised data. Updating the backup more frequently makes it easier and quicker to fix the problem. Cloud-based cyber security risk assessment solutions backup your data and include security features to block unauthorised access.
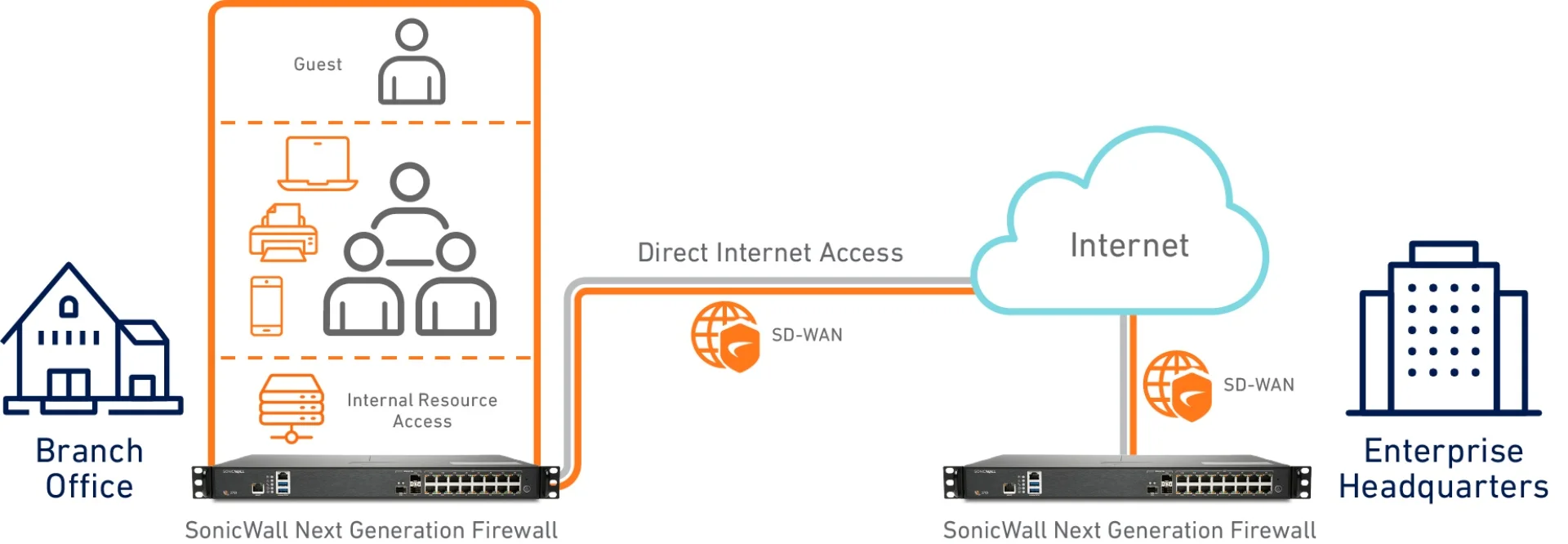
The firewall is considered the core of any cyber security solution. It is the single most important tool your business must own. When your website or web application is connected to the Internet, your firewall monitors the network traffic.
Recognises vulnerabilities in businesses
Cyber security assessments show which parts of the security measures are weak and which parts of the system can be targeted by attackers.
Allows businesses to review security controls
An assessment of cyber security can help one see how efficient their security controls are and how they can improve them.
Ensures compliance with industry-related standards
Companies can ensure their organisation fulfils all the correlated compliance requirements before it is too late.
Confidence among consumers
Your customers will trust you if you can assure them that their personal information will not be compromised.
A baseline of security
Upon understanding your security controls, you will know what is working and what isn't. By establishing a baseline, you'll be able to customise an assessment of your organisation.
Assess the scope of the overall cyber security assessment – Determine the full spectrum of the cyber security risk assessment by identifying all enterprise assets that require evaluation. Some security experts recommend limiting the scope of an evaluation to one type of asset rather than trying to do it all at once.
Analyse Your Data for Value – There are different types of data. Your organisation’s data collection and storage capabilities may be vast, but some data is more important than others. Therefore, the second step is to determine which data needs the most protection.
Identify and Prioritize Your Assets –If you have identified the data, you can break them down into categories and then prioritise those categories based on how important it is to keep them secure. Creating a cyber security plan with the best methods to secure sensitive information is a must for your IT team.
Identify Threats – A risk assessment process begins with identifying which data (and associated assets) needs to be protected the most. After that, you can contemplate and calculate various loss scenarios for future decisions.
Identify Vulnerabilities – Start searching for vulnerabilities within your information systems once you have a better idea of your current security posture. To determine whether there is any vulnerability that leaves your company exposed, you should perform a penetration test.



